Deepfake Threats in 2026: Why Face Verification Must Evolve or Fail
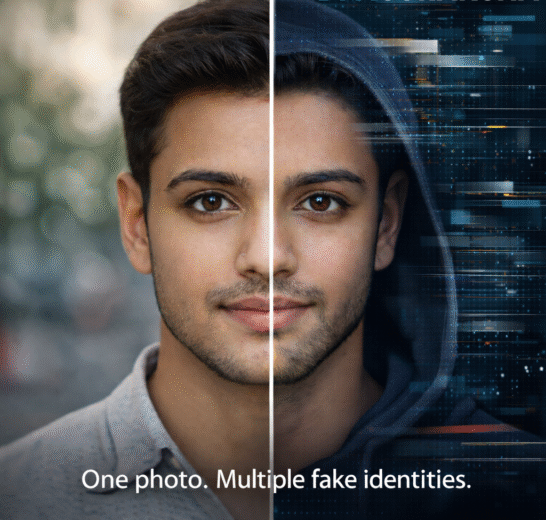
Deepfakes are no longer a future risk—they are present-day weapon. By 2026, AI-generated faces are realistic enough to bypass outdated identity systems that still depend on visual similarity, static images,…